Kids today are growing up in a world that is more connected than ever. That sounds great until you realize it also means more exposure to online threats. Social engineering is one of the sneakiest dangers out there. It does not rely on hacking software. It targets people directly, using tricks and manipulation to get what the attacker wants.
For school students, this is a serious concern. Scammers know that young people tend to trust quickly. They also know that students may not recognize the warning signs. The good news is that awareness works. Teaching students how to spot these tactics early can make a real difference.
This article walks through what social engineering looks like in a school context. It also covers why early education matters, what tactics to watch for, and how schools can build stronger defenses.
What Social Engineering Looks Like for K-12 Students
Most people picture hackers when they think of cyber threats. Social engineering is different. It is less about technology and more about human psychology. An attacker might pretend to be a friend, a teacher, or even a tech support agent. The goal is always the same: get the target to hand over information or access.
For K-12 students, this often shows up in everyday digital spaces. A fake profile might slide into a student's Instagram DMs. An email might claim the student won a prize. A text might pretend to be from the school asking for personal details. These are not random. They are calculated.
Students are especially vulnerable because they are still developing critical thinking skills. They are also eager to fit in and be helpful, which attackers exploit. A student who gets a message from what looks like a classmate asking for their login details might not think twice. That is exactly what makes this so dangerous.
Why Students Benefit From Learning Social Engineering Early
Think about it this way: you would not wait until a child is in a car accident to teach them road safety. The same logic applies here. Learning about social engineering early gives students a framework they can use for life.
When students understand how manipulation works, they become harder to trick. They start asking questions. They pause before clicking links. They check before sharing personal information. These habits do not just protect them now. They carry into adulthood, college, and eventually the workplace.
There is also a community benefit. A student who knows what phishing looks like can warn their friends. One informed student can protect a whole group. Schools that invest in this education are not just protecting data. They are building a generation of people who are harder to manipulate.
Research consistently shows that human error is the leading cause of data breaches. That pattern starts early. Teaching students to be cautious is one of the most practical investments a school can make.
Common Social Engineering Tactics Students Should Recognize
Phishing and Its Many Forms
Phishing is the most common tactic students will encounter. It involves fake messages designed to look legitimate. These messages might come through email, text, or social media. They usually create urgency. "Your account will be locked." "Click here to claim your reward." That pressure is intentional. It is meant to stop you from thinking clearly.
Students need to know that legitimate organizations rarely ask for passwords or sensitive information through a message. If something feels rushed or too good to be true, that is a signal to slow down. Looking at the sender's email address, checking for spelling errors, and refusing to click unfamiliar links are all practical first steps.
Pretexting and Impersonation
Pretexting is when someone creates a fictional scenario to gain trust. For students, this might look like a person online claiming to be a school administrator needing verification of their student ID. It could also be someone pretending to be a classmate who "forgot" their login details.
Impersonation is closely related. Attackers often clone social media accounts and reach out to the original person's contacts. The fake account looks almost identical to the real one. Students who do not look closely might assume they are talking to someone they know.
Baiting and Quid Pro Quo
Baiting involves offering something appealing in exchange for information or access. A free game download, a gift card, or exclusive content can all be used as bait. Students who click these links may unknowingly install malware or give away login credentials.
Quid pro quo attacks work similarly. An attacker might offer to help a student with homework in exchange for account access. The exchange feels fair, which is what makes it effective. Teaching students that nothing online is truly free is a lesson worth repeating.
Practical Ways Schools and Teachers Can Prepare Students
Bringing Awareness Into the Classroom
The classroom is the best place to start this conversation. Teachers do not need to be cybersecurity experts to make an impact. Simple discussions about online safety can open students' eyes to risks they never considered.
Role-playing scenarios work particularly well. A teacher might present a fake phishing email and ask students to identify what looks suspicious. This kind of exercise turns an abstract concept into something students can see and engage with. It sticks far longer than a lecture alone.
Schools should also bring in guest speakers where possible. IT professionals, cybersecurity educators, and even law enforcement officers can speak to students in ways that feel real and credible. Hearing from someone who works in the field adds weight to the lesson.
Partnering With Parents and Guardians
Schools cannot do this work alone. Parents play a huge role in reinforcing what students learn. When families are informed, the lessons taught in school extend into the home environment.
Schools can host parent information nights focused on digital safety. Newsletters and school apps can share tips that parents can discuss with their kids. The goal is to create a consistent message. When students hear the same guidance from both school and home, it becomes part of how they think.
Technical Steps That Strengthen Student Awareness
Using Simulated Phishing Exercises
One of the most effective tools available is simulated phishing. Schools can work with IT teams or cybersecurity providers to send fake phishing emails to students. The goal is not to embarrass anyone. It is to teach through experience.
When a student clicks a simulated phishing link, they get an immediate lesson rather than a real consequence. They see what they missed. They learn what to look for next time. Studies show that simulated phishing programs significantly reduce the rate at which people fall for real attacks over time.
Implementing Clear Digital Policies
Students need clear rules about what is and is not acceptable online behavior. Acceptable use policies should be written in plain language. They should be explained to students, not just handed out and forgotten.
Policies should cover things like password sharing, account access, and how to report suspicious messages. When students know the rules and understand why they exist, they are more likely to follow them. They are also more likely to speak up when something does not feel right.
Building a Safer School Culture
Culture matters more than policy. A school can have the best rules in the world, but if students do not feel safe reporting threats, those rules mean little. Building a culture of openness is essential.
Students should feel comfortable telling a teacher or administrator when something suspicious happens online. That requires trust. It also requires that adults respond without judgment. If a student reports clicking a bad link and gets punished, other students will stay quiet next time.
Schools should celebrate good digital citizenship. Recognizing students who report threats or help peers stay safe sends a powerful message. It shows that security is a shared responsibility, not just a rule from above.
Peer education programs can also be powerful. Older students trained in digital safety can lead workshops for younger ones. Hearing from a fellow student often lands differently than hearing from an adult. It feels more relevant and less like a lecture.
Staff training is equally important. Teachers and administrators are also targets of social engineering attacks. When staff are informed, they model good behavior and are better equipped to recognize threats that affect the entire school community.
Conclusion
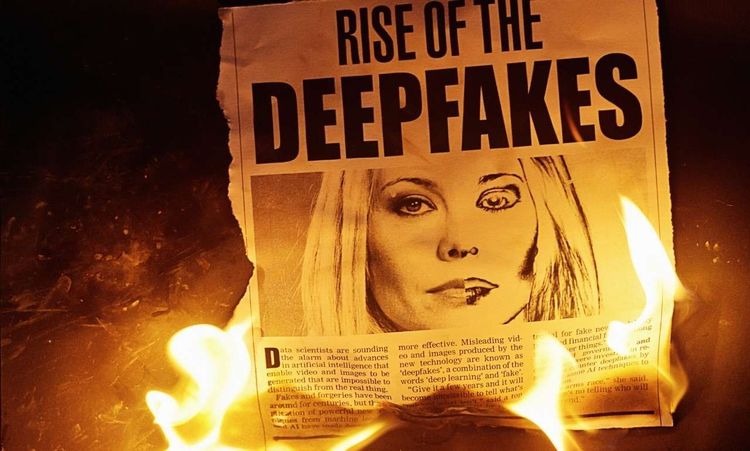
Social engineering is not going away. If anything, it is getting more sophisticated. Attackers are using AI tools to create more convincing messages and more believable fake identities. The threats students face today are more polished than ever before.
That is exactly why this education cannot wait. Schools, teachers, and parents all have a role to play. When students learn to pause, question, and verify, they become far harder to manipulate. That skill protects them in school, in college, and throughout their careers.
Start the conversation today. Ask your students what they would do if they received a suspicious message. You might be surprised by how much they already know, and how much they still need to learn.